Home / Law / Fraud Investigation: Making a Difference / Undertaking an investigation – Gathering evidence

Reach your personal and professional goals
Unlock access to hundreds of expert online courses and degrees from top universities and educators to gain accredited qualifications and professional CV-building certificates.
Join over 18 million learners to launch, switch or build upon your career, all at your own pace, across a wide range of topic areas.

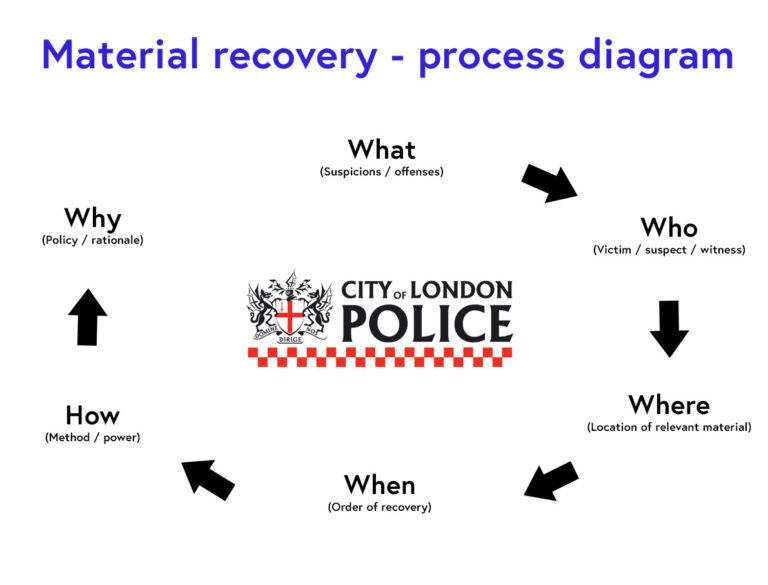
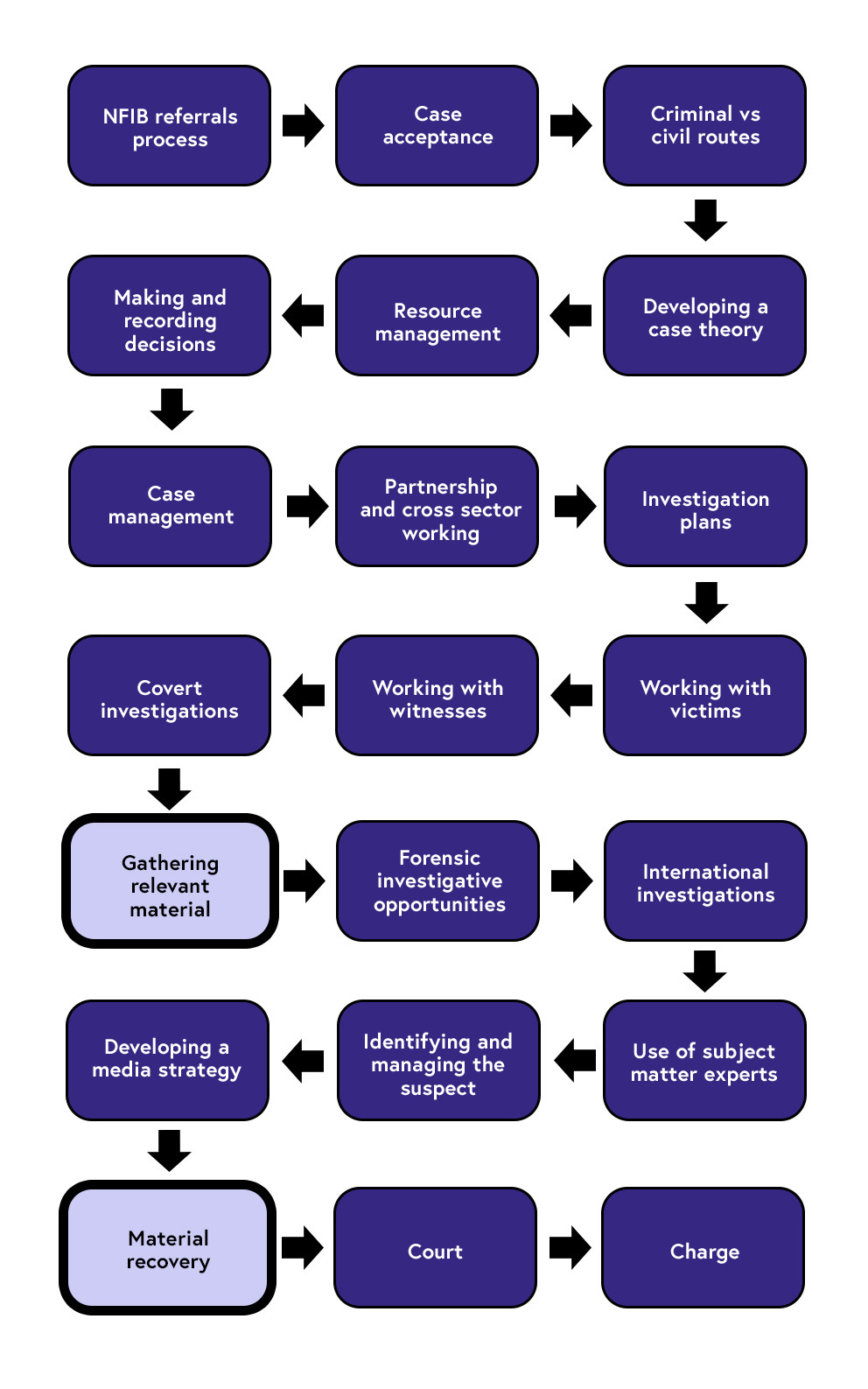 Case acceptance > Criminal vs civil routes > Developing a case theory > Resource management > Making and recording decisions > Case management > Partnership and cross sector working > Investigation plans > Working with victims > Working with witnesses > Covert investigations > Gathering relevant material (highlighted) > Forensic investigative opportunities > International investigations > Use of subject matter experts > Identifying and managing the suspect > Developing a media strategy > Material recovery (hihglighted) > Court > Charge.”>
Case acceptance > Criminal vs civil routes > Developing a case theory > Resource management > Making and recording decisions > Case management > Partnership and cross sector working > Investigation plans > Working with victims > Working with witnesses > Covert investigations > Gathering relevant material (highlighted) > Forensic investigative opportunities > International investigations > Use of subject matter experts > Identifying and managing the suspect > Developing a media strategy > Material recovery (hihglighted) > Court > Charge.”>